Icostamp: A Complete Guide to Its Meaning, Uses, and Growing Digital Relevance
In today’s rapidly evolving digital landscape, new terms and platforms frequently emerge, often carrying multiple meanings depending on their context. One such term gaining attention across blogs, business platforms, and tech discussions is “Icostamp.” While it may appear to be a single product or service at first glance, Icostamp is actually a multi-dimensional concept that spans digital verification, blockchain, marketing, and business development.
This article provides a comprehensive and in-depth exploration of Icostamp, including its definitions, applications, benefits, challenges, and future potential.
What is Icostamp?
Icostamp is not a universally standardized tool or platform. Instead, it is a broad digital concept or brand term used in different industries. In most contexts, it refers to systems or platforms that focus on:
- Digital verification and authentication
- Blockchain-based timestamping
- ICO (Initial Coin Offering) validation
- Business tools and knowledge platforms
- Marketing analytics and automation
At its core, Icostamp revolves around one central idea:
👉 Building trust, transparency, and efficiency in digital environments.
Origins and Concept Behind Icostamp
The word “Icostamp” appears to be a combination of two elements:
- ICO (Initial Coin Offering) – a fundraising method in the cryptocurrency space
- Stamp – symbolizing approval, verification, or authentication
Together, the term suggests a system that validates, certifies, or verifies digital information or projects, especially in modern online ecosystems.
Over time, the usage of Icostamp has expanded beyond crypto into broader areas like document management, business consulting, and digital marketing.
Different Interpretations of Icostamp
1. Digital Document Stamping Tool
One of the most straightforward uses of Icostamp is as a digital stamping solution. In this context, it functions as a tool that allows users to:
- Apply electronic stamps to documents
- Authenticate official files
- Replace traditional ink-based stamping methods
This is particularly useful for businesses and organizations that aim to:
- Reduce paperwork
- Speed up approvals
- Maintain digital records
Such tools often include features like timestamping, signature verification, and secure storage, making them ideal for modern workflows.
2. Blockchain-Based Verification System
Another prominent interpretation links Icostamp with blockchain technology. In this role, it acts as a system that:
- Records data timestamps on a blockchain
- Ensures that information cannot be altered
- Provides proof of authenticity
This is especially valuable for:
- Legal documents
- Intellectual property
- Financial transactions
Because blockchain is decentralized and tamper-resistant, Icostamp-like solutions offer high levels of security and trust, which are critical in today’s digital economy.
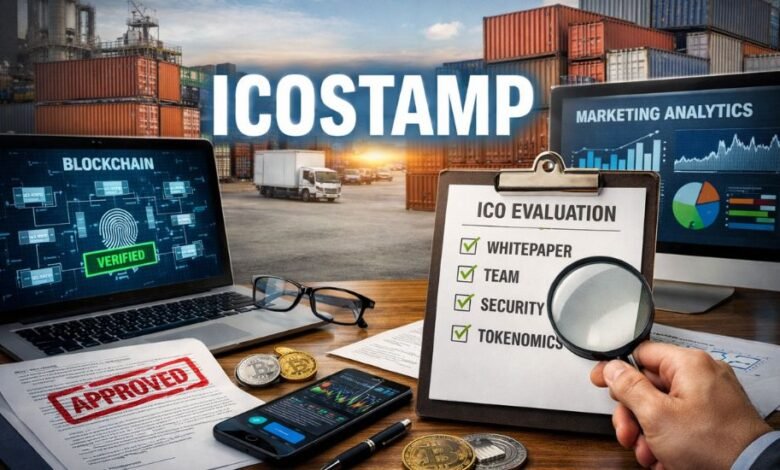
3. ICO Rating and Certification Platform
In the cryptocurrency space, Icostamp is sometimes described as a rating or evaluation system for ICO projects. These platforms analyze various aspects of a project, such as:
- Team credibility
- Technical whitepapers
- Token economics
- Security measures
The goal is to help investors identify legitimate opportunities and avoid scams. Given the risks associated with crypto investments, such evaluation systems play a key role in building investor confidence.
4. Digital Marketing and Analytics Tool
Some sources describe Icostamp as a marketing technology platform that helps businesses optimize their digital strategies. Features may include:
- Audience segmentation
- Campaign performance tracking
- Data-driven insights
- Automated scheduling
In this context, Icostamp enables companies to:
- Improve engagement
- Increase conversion rates
- Make smarter marketing decisions
This aligns with the broader trend of data-driven marketing, where analytics play a central role in business growth.
5. Business Knowledge and Resource Platform
Icostamp is also associated with educational and business-oriented platforms that provide guidance for entrepreneurs and startups. These platforms often focus on:
- Business planning
- Financial management
- Marketing strategies
- Scaling operations
By offering structured insights, Icostamp helps individuals and businesses navigate complex challenges and achieve sustainable growth.
6. Supply Chain and Product Tracking Solution
Another emerging interpretation connects Icostamp with supply chain management. In this role, it helps businesses:
- Track products across different stages
- Ensure compliance with regulations
- Maintain transparency
This is particularly useful in industries where authenticity and traceability are critical, such as:
- Pharmaceuticals
- Food production
- Manufacturing
Key Features of Icostamp
Despite its multiple meanings, several common features define Icostamp across different applications:
1. Digital Authentication
Ensures that documents, data, or transactions are genuine and verifiable.
2. Transparency
Provides clear and traceable records, especially when integrated with blockchain.
3. Automation
Reduces manual processes, saving time and effort.
4. Security
Protects sensitive information through encryption and decentralized systems.
5. Scalability
Adapts to various industries and use cases, from startups to large enterprises.
Benefits of Using Icostamp
1. Improved Efficiency
By digitizing processes, Icostamp eliminates the need for manual paperwork and speeds up operations.
2. Enhanced Security
Advanced technologies like blockchain ensure that data cannot be tampered with.
3. Cost Reduction
Businesses can save money by reducing reliance on physical resources and manual labor.
4. Increased Trust
Verification systems build confidence among users, clients, and investors.
5. Better Decision-Making
Data analytics tools provide valuable insights for strategic planning.
Challenges and Limitations
While Icostamp offers numerous advantages, it also comes with certain challenges:
1. Lack of Standardization
The term is used in multiple contexts, which can create confusion.
2. Varying Reliability
Not all platforms labeled as Icostamp are equally trustworthy.
3. Technical Complexity
Some implementations, especially those involving blockchain, may require specialized knowledge.
4. Adoption Barriers
Businesses may face resistance when transitioning from traditional systems to digital solutions.
Use Cases of Icostamp
1. Corporate Documentation
Companies use digital stamps to verify contracts, agreements, and internal records.
2. Legal and Compliance
Ensures authenticity and compliance with regulatory standards.
3. Cryptocurrency Investments
Helps investors evaluate and verify ICO projects.
4. Marketing Campaigns
Enables businesses to track performance and optimize strategies.
5. Supply Chain Management
Provides transparency and traceability for products.
Future of Icostamp
As digital transformation continues to reshape industries, the relevance of Icostamp is expected to grow. Key trends include:
- Integration with AI and automation tools
- Expansion of blockchain applications
- Increased demand for digital verification systems
- Growth in remote and paperless workflows
In the future, Icostamp could evolve into a standardized ecosystem that combines multiple functionalities into a single platform, offering comprehensive solutions for businesses and individuals alike.
Why Icostamp Matters in Today’s Digital World
The digital age demands trust, speed, and efficiency. Whether it’s verifying a document, evaluating a crypto project, or optimizing a marketing campaign, Icostamp addresses these needs by providing:
- Reliable verification systems
- Transparent processes
- Scalable solutions
This makes it a valuable concept for anyone involved in business, technology, or digital innovation.
Final Thoughts
Icostamp is more than just a term—it represents a shift toward smarter, more secure, and efficient digital systems. While its exact meaning may vary depending on context, the underlying principles remain consistent: verification, trust, and innovation.
As businesses and technologies continue to evolve, Icostamp will likely play an increasingly important role in shaping the future of digital interactions.
If you’re exploring modern tools and concepts that enhance efficiency and trust, Icostamp is certainly worth understanding. For more insightful articles like this, visit marketblog, where we break down complex digital trends into clear and actionable knowledge.



